Digital Security Logs Covering 8x7x6x5x4x3x2x1 and Alerts Records
Digital security logs serve as a vital component in an organization’s cybersecurity framework. They meticulously document user interactions and system operations, including access logs and alerts. A systematic aggregation of these logs, particularly those covering 8x7x6x5x4x3x2x1, reveals critical insights into both system performance and vulnerabilities. Understanding the nuances of alert analysis can significantly enhance incident response strategies, prompting organizations to adopt more proactive security measures. The implications of this are profound.
The Role of Digital Security Logs in Threat Detection
Digital security logs serve as critical tools in the identification and mitigation of potential threats within an organization’s IT infrastructure.
By aggregating data relevant to user activities and system operations, these logs enhance threat intelligence capabilities.
Effective incident response relies on the insights gained from security logs, enabling organizations to swiftly address vulnerabilities and safeguard their digital environments against emerging threats.
Types of Records in Security Logs
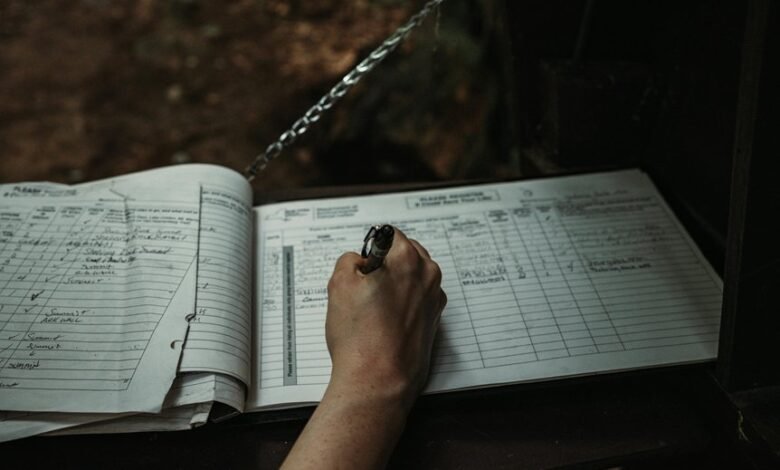
Security logs encompass a variety of record types that document user interactions, system events, and network activities.
Common log types include access logs, error logs, and audit trails, each utilizing distinct record formats.
These logs provide essential insights into system performance and security postures, allowing for comprehensive monitoring and investigation.
Understanding these differences is vital for effective data management and enhancing overall digital freedom.
Analyzing Alerts for Proactive Security Measures
While organizations often collect a plethora of security alerts, the true value lies in their analytical interpretation for proactive measures.
Effective alert prioritization enables security teams to focus on critical incidents, enhancing incident response capabilities.
Best Practices for Managing Security Logs
Effective management of security logs is essential for maintaining an organization’s overall cybersecurity posture.
Adhering to log retention policies ensures that data is preserved for necessary periods, facilitating audits and investigations. Organizations must align their practices with compliance requirements to avoid penalties.
Regularly reviewing and analyzing logs can help identify anomalies, ultimately enhancing security measures and safeguarding organizational freedom against potential threats.
Conclusion
In conclusion, digital security logs serve as the backbone of an organization’s cybersecurity framework, enabling effective threat detection and response. By systematically analyzing various record types and prioritizing alerts, organizations can stay one step ahead of potential vulnerabilities. Adopting best practices for log management not only enhances compliance but also fortifies the overall security posture. Ultimately, investing in robust log analysis allows organizations to turn the tide in their favor, effectively keeping cyber threats at bay.





